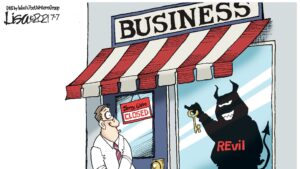
Welcome back to the truly not funny world of ransomware, where cybercriminals dare to make demands with all the subtlety of a bullhorn-wielding toddler in a candy store. Last week brought us some ransom-related shenanigans that would make even the most notorious hackers scratch their heads and wonder, “Did we do that?”
Boeing’s “Oops, We’ve Been LockedBit” Episode
In the latest episode of “Oops, We’ve Been LockedBit,” Boeing, yes, the same Boeing that builds those big flying tubes we call airplanes, found itself in a tight spot. The LockBit ransomware gang decided to give them a little visit and let’s just say they weren’t there for the in-flight snacks.
LockBit wasted no time in revealing their grand plans. They threatened to spill the beans on sensitive Boeing data unless the aerospace giant coughed up some cash by November 2. In their ransom note, the hackers said, “Give us the money, or we’ll start sharing your secrets faster than your Wi-Fi on an airplane.”
Boeing responded with a poker face, saying they were “assessing this claim.” Yeah, because when you’re potentially holding the secrets to the skies, you want to take your time and think it over. No rush, right?
LockBit – The Ransomware Rockstars
Now, let’s talk about LockBit, the ransomware rockstars who have been touring the criminal circuit since 2019. These guys are like the Houdinis of encryption, demanding ransoms bigger than a Hollywood blockbuster budget. We’re talking $50 million, folks, not pocket change.
Their list of victims reads like a who’s who of “Oops, We’ve Been LockedBit.” From SpaceX to Shakey’s Pizza (seriously, pizza places?), these guys have a knack for targeting the juiciest targets. They even tried to squeeze $70 million out of Taiwan Semiconductor Manufacturing Company (TSMC) in July. Maybe they thought they were ordering silicon chips instead of ransomware?
LockBit’s been so busy that they even introduced LockBit 3.0 last year and decided to spice things up with some macOS ransomware this year. Because why not diversify your criminal portfolio?
To add insult to injury, these hackers love playing hide and seek with security tools, exploiting remote desktop protocol, and spreading through Group Policy Objects. If only they put this much effort into a legitimate career, they could have been tech gurus.
The Great Ransomware Debate
Now, let’s get serious for a moment, or as serious as we can in the world of ransomware hilarity. There’s this ongoing debate about whether to pay the ransom or not. It’s like the age-old question: “To be or not to be?” But instead, it’s “To pay or not to pay?”
According to a survey, 83% of organizations admit to paying hackers following a ransomware attack. Some even forked over $100,000 or more. Hey, when your digital life is hanging by a thread, you might be willing to mortgage the office coffee machine.
But the debate rages on. Some say paying is like negotiating with cyber terrorists, while others argue it’s the quickest way to get your data back. It’s like trying to decide between the blue pill and the red pill in “The Matrix.” Decisions, decisions.
SEC’s Got the Scoop on SolarWinds
In another twist in the ransomware saga, the SEC charged SolarWinds and its CISO, Timothy G. Brown, with fraud. They were doing some creative storytelling about their cybersecurity prowess. When you’re a software services provider, that’s not a good look.
The SEC claims they misled investors, talking about cybersecurity protections like they were selling magic wands. Meanwhile, they were allegedly sweeping known risks under the rug. Oops, somebody forgot to read the fine print.
This case reminds us of the importance of transparency in publicly traded companies. It’s like telling your Tinder date you’re a supermodel when you’re a potato farmer. Honesty is key, people!
As for Apache ActiveMQ and the HelloKitty ransomware group, well, they decided to turn a critical vulnerability into a hacking circus. It’s like giving a toddler a chainsaw and hoping for the best. The ransomware business just keeps getting more bizarre.
In Conclusion
So, there you have it, folks, the wild and wacky world of ransomware, where hackers demand ransom like it’s a dinner reservation at a fancy restaurant. Remember, in this digital jungle, it’s always better to be prepared. Patch those vulnerabilities, protect your endpoints, and brace yourself for more ransomware rollercoasters. Because in the end, laughter is the best defense against cyber mayhem.
NOV
About the Author:
Online Security Expert Todd Laff reviews online hacks and security issues and how to protect yourself and secure your network.